3/6/2026


In the world of software development, a Full-Stack Developer is someone who understands the entire lifecycle of an application. They don't just care about the "Front-End" (the buttons you click) or the "Back-End" (the database where your info lives); they understand how every layer interacts to create a stable, secure environment.
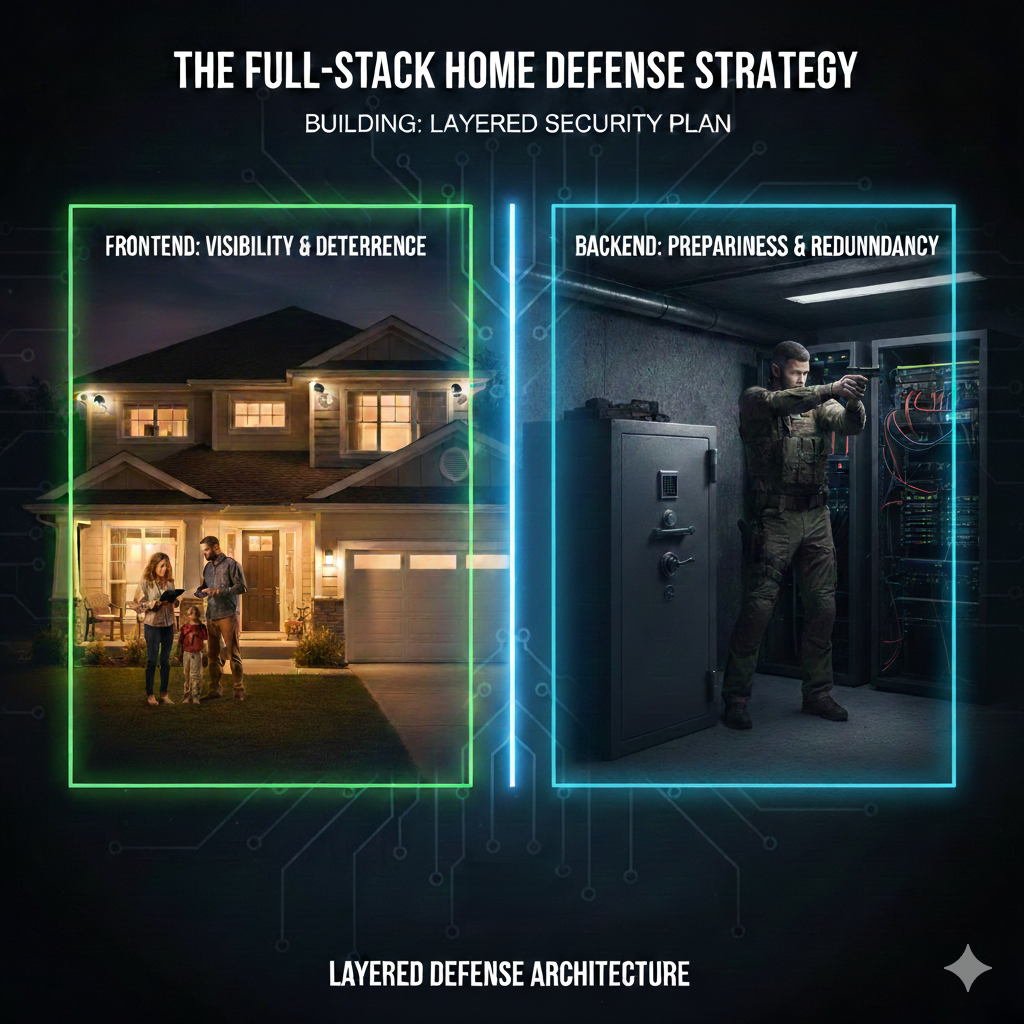
When it comes to your home, most people are "Front-End Only." They focus on the visual—a doorbell camera, a "Beware of Dog" sign, maybe a sturdy-looking deadbolt. But in a real-world "System Crash" (a home invasion or emergency), a pretty interface won't save you if the database is corrupted and the server is down.
To truly protect your family, you need a Full-Stack Defense Strategy.
In web dev, your Front-End is your first point of contact. It’s designed to guide legitimate users in and keep "bad requests" out. For your home, this is CPTED (Crime Prevention Through Environmental Design).
Middleware is the logic that sits between the user and the data. It monitors traffic and looks for anomalies.
This is where the actual "Data" lives—your family. If an intruder makes it past the Front-End and the Middleware, your Back-End Architecture is your last line of defense.
A beautiful website with a broken database is a failure. Similarly, a home with $2,000 worth of cameras but no "Safe Room" protocol or medical training is a disaster waiting to happen. Stop building "Security Theater" and start building a Full-Stack Defense. Hardened on the outside, resilient on the inside.
As we discussed in Week 3, Wi-Fi is a convenience, but it’s a security vulnerability. Most "Smart" cameras can be disabled by a $20 "Deauther" tool that jams the signal.
The Fix: Whenever possible, hardwire your security "Back-End" using Power over Ethernet (PoE). In the dev world, we know that "The Cloud" is just someone else's computer—keep your security local, hardwired, and under your control. A wire can't be jammed; it has to be cut, and a cut wire triggers a system alert
Next Week: The secret to excellence is... boring. Join in next week as I look into dry fire practicing.